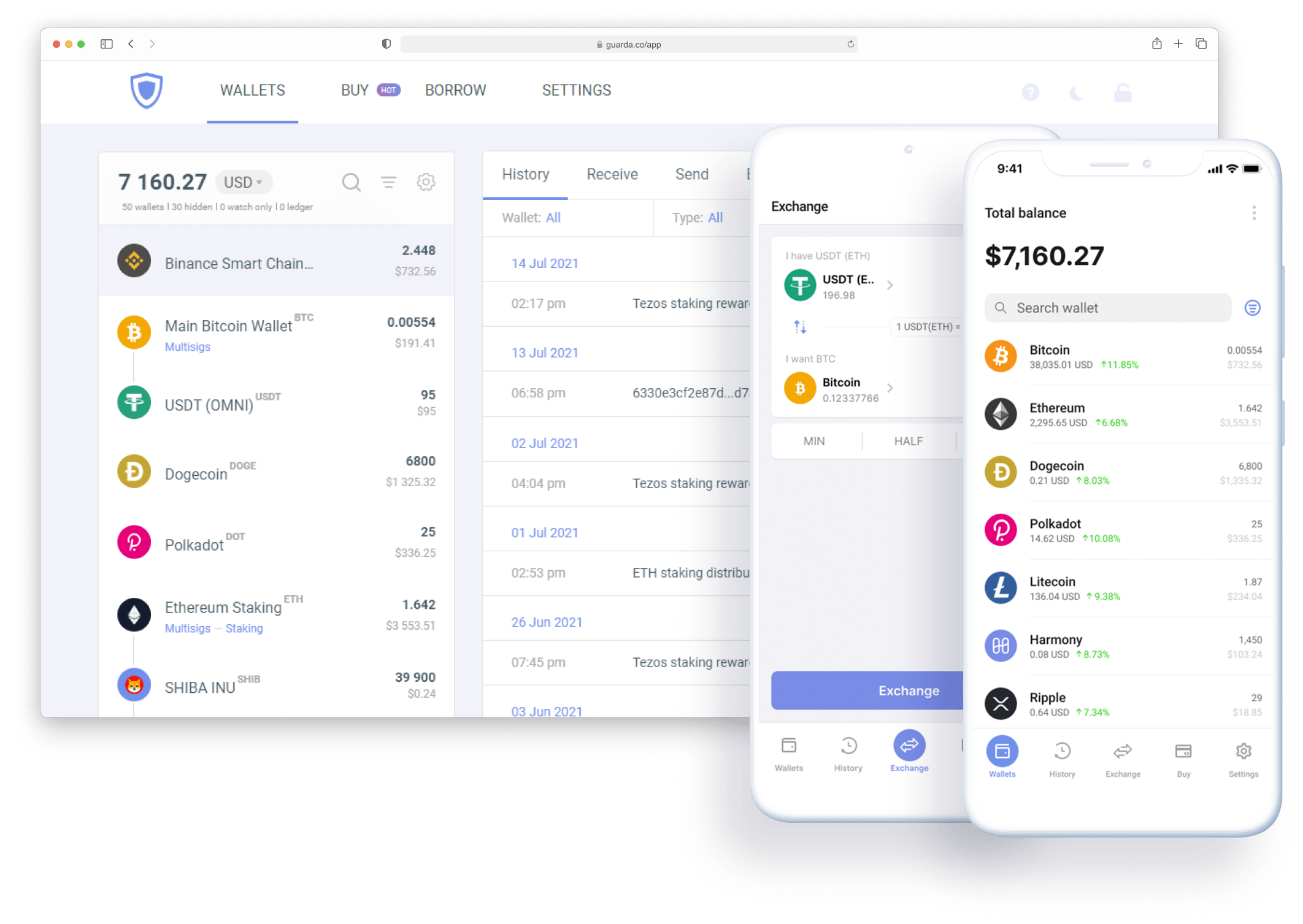
Support for over 70+ major blockchains & over 400K tokens of all leading protocols. Stay in complete control of your assets.
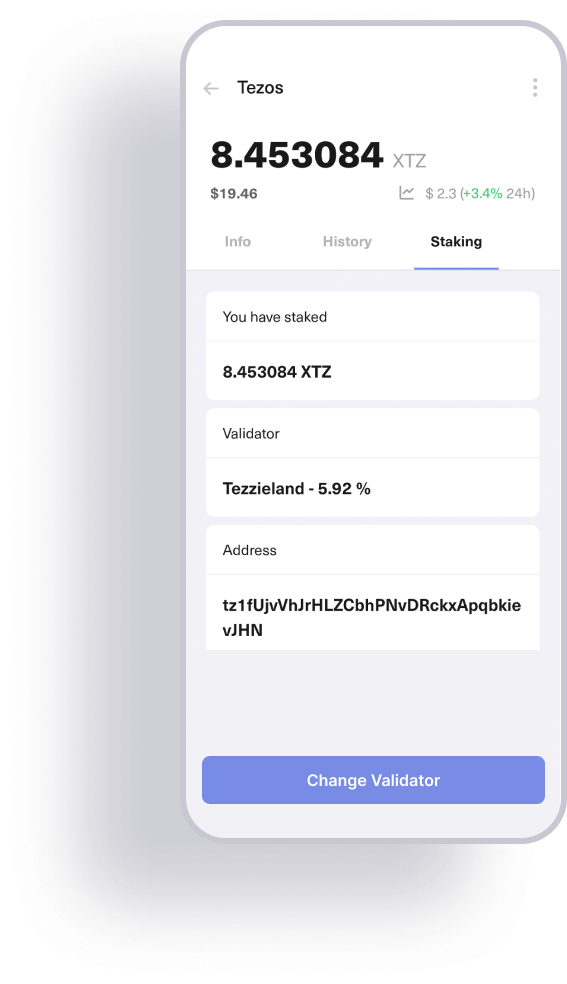
Earn with Staking
Lots of trending assets available for staking
Up to almost 40% annual yield
Exchange Crypto
Instant crypto exchange for over 50 coins using your Android or iOS wallet
Exchange Now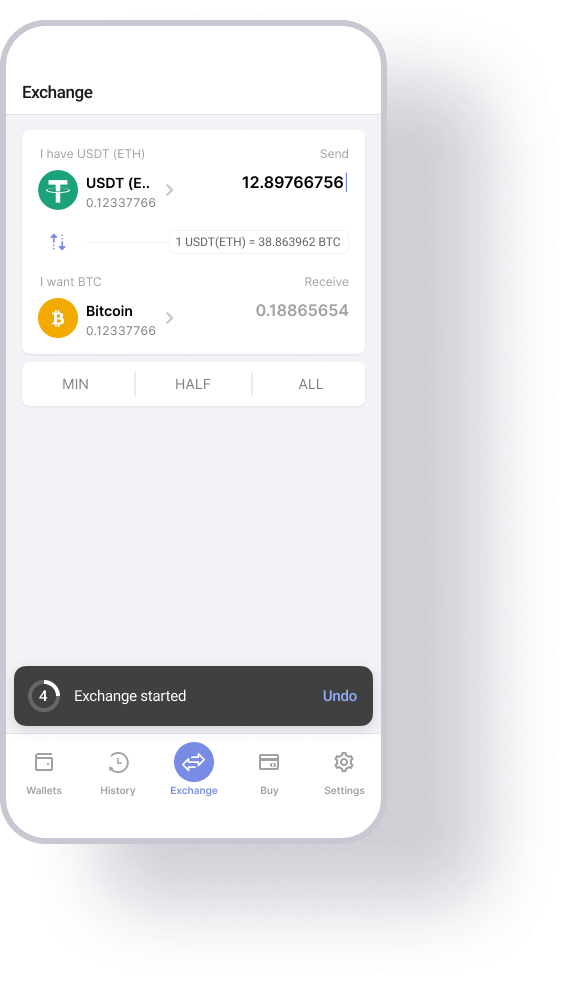
All Assets In
One Secure Multi Crypto Wallet
Be In Charge of Your Crypto
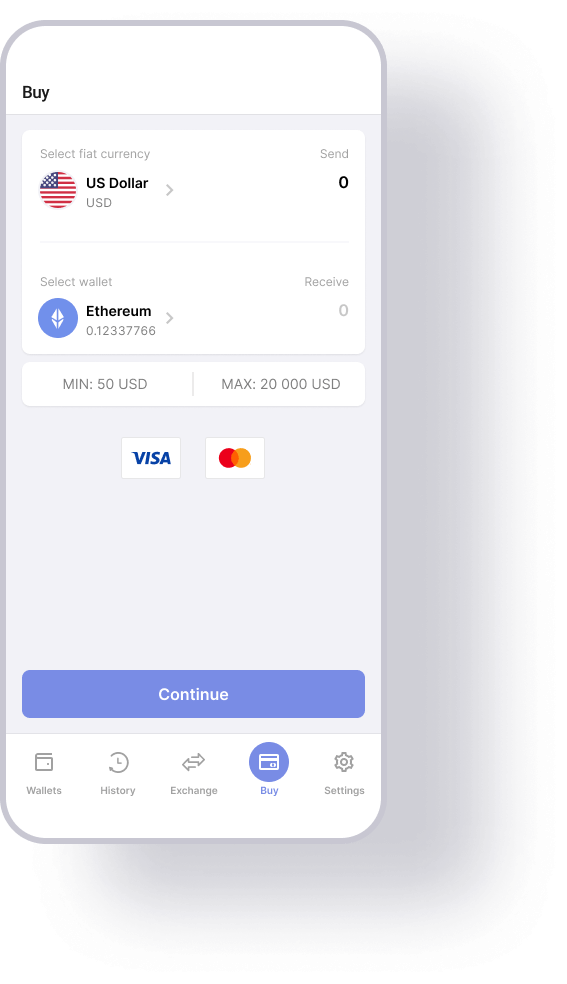
Guarda is an ultimate solution for modern crypto management. You can do it all from the comfort of one single app. Earn with staking, Purchase, Instantly Exchange at best rates, get crypto loans, add extra security layer with Multisignature, and the list goes on.
Get StartedFeatured in Media
Neat!
Thank you for the download 🔥
Thank you for the download 🔥
We love having you onboard Guarda Wallet – have a blast managing your coins and be sure to subscribe to our updates. Big news ahead!
Subscribe to news
We will only use your email to deliver news and updates. For more information, please see our Privacy Policy.
Download
Follow Us